Why are all organizations at risk?
Internal Access to Data
Ensuring the sensitive data within your organization is in the right hands is crucial to keeping that data from being maliciously exposed. Internal employees can maliciously act out for many reasons and expose the organization's sensitive data to a number of sources, which can destroy the organization.
Growth of Data
The digital landscape is doubling in size every two years. By 2020, the data we create and copy annually will reach 44 trillion gigabytes. With so much data to manage, one of the biggest challenges is knowing where your sensitive data resides.
Increasing Compliance Requirements
Compliance affects every business, no matter the vertical or size. Organization's need to prove that they are implementing the required measures to keep their customer's sensitive data safe. Failure to do so can result in extremely hefty fines which can ultimately take down small to mediurn sized businesses.
How can organizations protect their sensitive data?
Organizations can implement a data loss prevention software to understand the structure and location of their high value data within their organization. Data Loss Prevention software will enable businesses of all sizes to analyze the movement and storage of sensitive data across their network and beyond, as well as protect sensitive information from exposure by employees and third parties. By building an action plan, organizations can keep their sensitive data secure in today's digital transformation.
What will I gain using a DLP solution?
You can monitor and act on data in motion, data in use, and data at rest.
Data in motion
Scan and monitor outbound web and email traffic.
- Data transfers over HTTP, HTTPS protocols are intercepted.
- All mail is inspected using a content filter.
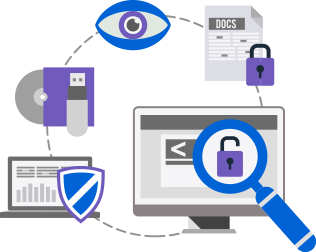
Data in use
Monitor how your data is used on endpoints, discover sensitive data stored on cornputers and laptops and control the use of USB devices, screenshots, clipboard, printing, CD/DVDs, etc.
Data at rest
Easily scan servers and databases for sensitive information.
- Data which resides at a workstation, notebooks and host computers are traced and inspected.
- Data which resides at file servers, network storages, Windows shares, etc. are traced and inspected.
Take action
- Remove data that is stored, used inappropriately or is no longer needed
- Take note that an action occurred but don't inform the user
- Log the event and store a copy of the file on the DLP server
- Block users from specific actions and keep a copy of the event
What data do you want to protect?
Credit card information?
Identifiable health information?
Personal data?
Financial data?
Corporate Secrets?
Begin discovering, monitoring and controlling the movement and storage of your sensitive data now.
Protect Data NowLearn more about DLP here

Multimedia Apps and Growing Threat About Data Protection
Although online users increasingly rely on mobile applications for their daily activities and needs, the…..

Data Leak Prevention – Are Enterprise On The Right Path?
A hacker in mask or hacker in a hoodie are symbols identical to privacy breaches……

Business Data Loss Prevention and How To Be Safe
Data loss is a constant threat in today’s business world. Up to 50% of the…..